Tuesday started fine, train down the capital a chance to meet up with the London work team. So far so good, until a colleague suggested a ‘quiet’ drink after work. Ended up not being too quiet after all.
With Wednesday starting off with ‘why?….’, I found some energy and headed for Security BSides London. As I’d already reconnoitered the location on Tuesday getting to the location was a breeze, only to find the door locked. Javvad Malik to the rescue, arrived at same time and managed to call one of the organisers to let us in. After brief introductions all round I met Soraya Iggy in person for the first time, absolutely nothing like I was expecting but great in every way. After receiving goodie bag (and getting repeated grief from Iggy to change into con shirt) I enjoyed some good geek chat whilst watching the venue fill.
After the official opening of the event, I headed upstairs to track two, which started with Aaron Finnon discussing DNS tunneling techniques. I was looking forward to this talk as I’d got half of the information over a drink after Aaron gave his famous SSL talk when OWASP Leeds travelled to Newcastle. My main takeaway from the discussion was that with the use of some relatively simple tools it can be relatively simple to bypass most captive wireless portals if they aren’t sufficiently tying down egress traffic. First on my to-do list of ‘I wonder what happens if you try this in my environment?’.
Second session was David Rook and Chris Wysopal, discussing ‘Jedi Mind’ tricks for building security programs. Having watched recordings of both presents from other events I was looking forward to getting the live experience, and neither disappointed. The presentation was great and I took a lot away for how to both discuss security issues with non-infosec people, and how to talk about the problems in business terms to get buy-in to effect real change in an organisation. I was somewhat surprised, as this started a trend of the event with my favourite presentations being non-technical in nature.
Third session was one that I’d heard a few people dismiss before the event as being a bit lame. I’d already picked it out as my preferred session for this timeslot (it was a tough call, other track was Justin Clark discuss web app attacks, but the end would have over run with the next talk I wanted to see). I’m glad I didn’t let the naysayers dissuade me, Ellen Moar and Colin McLean did a great job demonstrating just how simple it is for anyone with basic computer knowledge (script kiddie) to cut and paste their way past defensive countermeasures (AV). Content wasn’t anything groundbreaking (which is why I think some weren’t keen), but I think it’s the first time I’ve actually seen someone ‘prove’ what we all accept as gospel. Scary stuff.
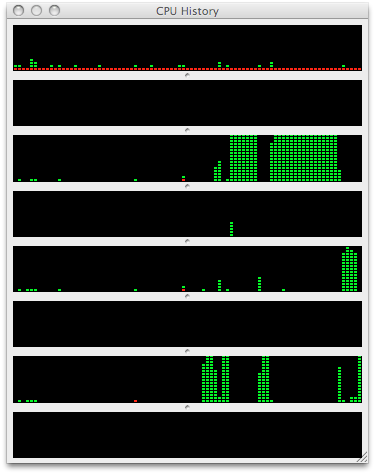
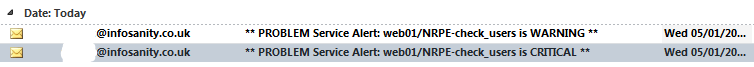
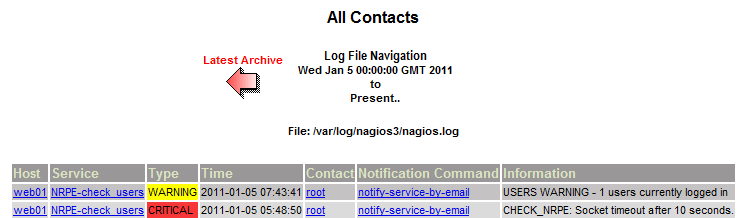
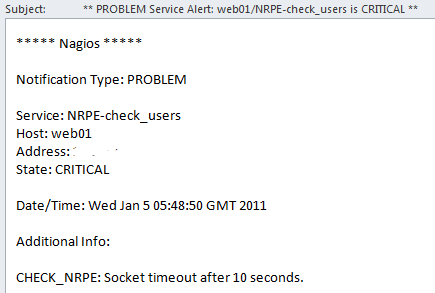
Final session of the morning was Xavier Mertens discuss logging and event management. Not the most thrilling of topics I’ll admit, but it’s something that so few organisations seem to get right I was interested to find out if there were any ‘better’ ways that could improve the process. Not only are there apparently better ways, but apparently there are also free better ways, so I’m going to talk a closer look at OSSEC.
After lunch Steve Lord provided an ‘interesting’ look into different types/levels of pentester and what it means to be in the industry. The talk received a lot of laughs, but in hindsight I wish I seen a talk with more technical content. For me, bsides was for education and networking, I’ll leave comedy to the comedians.
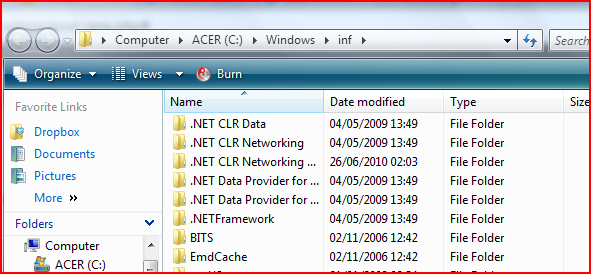
Next talk was better, Wicked Clown, expanding on his Brucon Lightening talk showing how to break out of a restricted RDP session. This was a great presentation, and was another attack to add to my ‘what if’ to-do list. More importantly he also provided a simple fix to prevent the attack vector, considering it’s a single checkbox, and the workaround breaks how most would ‘expect’ the service to behave I’ll echo his confusion as to why Microsoft don’t have the checkbox ticked by default. Perhaps secure out of the box is too much to ask?
David Rook took to the stage again, this time alone and discussing static code analysis with Agnitio. I’d taken a look at Agnitio since David released it, but as I’m not much of a dev (see the utilities I release for proof…) haven’t been able to try it in anger. If you’re interested, the talk slides are available on the Security Ninja blog. If the tool can reach the stated end of it’s road map of being the ‘Burp Suite of static analysis’ then it should be a fantastic tool.
Next talk I saw was Manuel demo (reverse~re)engineering of DRM within Android applications. I found the talk fascinating, mostly by how quick Manuel was able to put the pieces of the puzzle together and bypass the protections put in place to do exactly what he was attempting. Whilst the presentation was good, it was one of those where you felt your comparative IQ drop as you see black magic being wielded at the keyboard before your eyes.
The event finished with ‘Security YMCA’, words cannot describe this ‘experience’ so I won’t attempt to, and leave you with this YouTube video. (WARNING: once seen, cannot be unseen). Unfortunately trying to hide at the back didn’t help in the end, so I must apologise to Ellen as I managed to say thanks for an interesting talk by subjecting her to my ‘singing’ attempts. To ensure the the guilty aren’t protected, those at the front assaulting your sensors are:
we don’t have a solution for the iPhone, as it’s a secure platform why bother?