As the world (or at least, myself) begins to emerge from Lockdown, in-person events are returning. For me, this was initiated with an excellent trip to Manchester, experiencing Matillion’s Super All Hands gathering, meeting with new colleagues that had until that point merely been faces on a collage of Zoom tiles. As part of the […]
Category archives: InfoSec
Automating infrastructure code audits with tfsec
Unless you’ve been living under a rock for the last few years, you’ll know a few things about the Cloud: Functionality and capabilities released by Cloud vendors are expanding at an exponential rate. DevOps paradigm is (seemingly) here to stay – the several cold days of building physical hardware sat on the floor of a […]
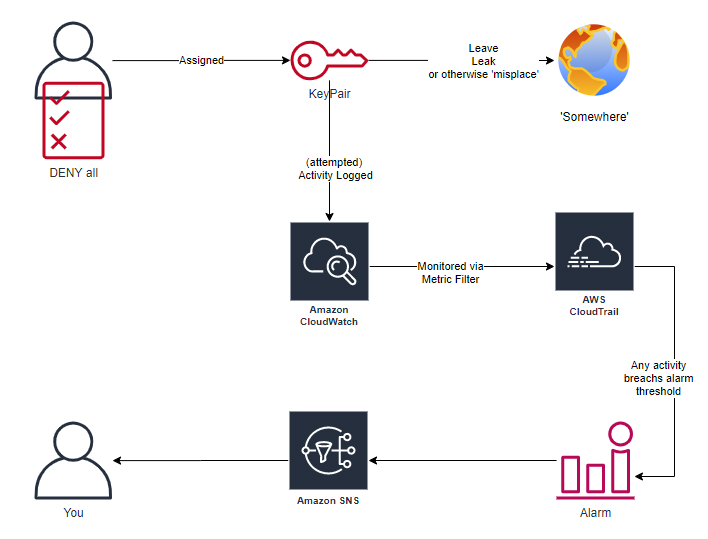
AWS HoneyUsers
Deception technology and techniques are having a resurgence, expanding beyond the ‘traditional’ high/low- interaction honeypots, into honeyfiles, honeytokens and (as you may have guessed from title) honeyusers. Today is the culmination of a “what if?” idea I’d been thinking for years, actually started working on earlier in the year (but then 2020 happened), but is […]
A Northern Geek's trip South West
June has been a busy month, hot on the heels from BSides London (review here), I again found myself on a train BSides-bound, this time heading for Liverpool. Before getting to the tech, I’ll point out that this was my first time in Liverpool. After a very brief visit I found the city to be […]
A Northern Geek's Trip South – 2019 edition
How time flies; and with it, another BSides London is a long distant memory. My itinerary for the pilgrimage South was familiar, mostly following a well worn pattern InfoSec Europe Tuesday BSides itself Wednesday Thursday? Recovery time in the capital, before heading for the train back to (my) civilised society. And throughout: a generous smattering […]
Google Glass: New threat or business as usual?
Woke this morning to find several articles covering the release of a short script designed to locate and ultimately block wearers of Google Glass from accessing a wireless network. This was apparently released in response to someone else’s discomfort from knowing there was a wearer of Google Glass in an audience, mostly due to the recording/stream capabilities. […]
Stupidity, begets stupidity – and no security
I realised whilst at work today that my credit card wasn’t in my wallet, after hoping against hope that it would be in yesterday’s trouser pocket when I got home I had to accept that it was lost. Far from the brightest thing I’ve done today, especially given the time of year. So I did […]
Online Bank Cards
The reaction most people have when you point out people are naive enough to post pictures of credit and debit cards online is to laugh, surely no one could be that unaware of the risks. But the fact is that the situation has become that common place that a number of Twitter accounts have been […]
ms12-020 mitigations
This week has been an interesting one for followers of the info-sec arena. On Tuesday Microsoft released a patch and security bulletin for MS12-020 for a critical flaw in remote desktop protocol, allowing for remote code execution without the need to authenticate to the target system first. Since the patch was released the good, the bad […]
HoneyD network architecture
I was recently asked about the network configuration I use for my honeyd sensor. As I now have a pretty(ish) network diagram showing my setup as a result, decided sharing is caring.